Open Container Initiative (OCI) Standard, Image Spec
Table of Contents
The Open Container Initiative (OCI) standard is an open standard for Linux containers. As born in 2013, Docker has been a de-facto standard of Linux container framework, but the OCI standard was born for a need of open standard, based on the Docker manifest. As the standard is based on Docker manifest, its specifications and structures are very similar to Dockers’, enabling providing compatibilities between Docker and OCI-based container frameworks.
The official website says it contains two specifications (the Image Spec and the Runtime Spec), however, its Github repository actually contains three specification: the Image Spec, the Runtime Spec, and the Distribution Spec. That may be because that distribution is currently out of scope on the OCI Scope Table [link].
Image Spec #
The OCI Image Spec is based on Docker Image Manifest Version 2.2. The architecture is very similar; hence docker images are convertible to the corresponding OCI image by using skopeo utility.
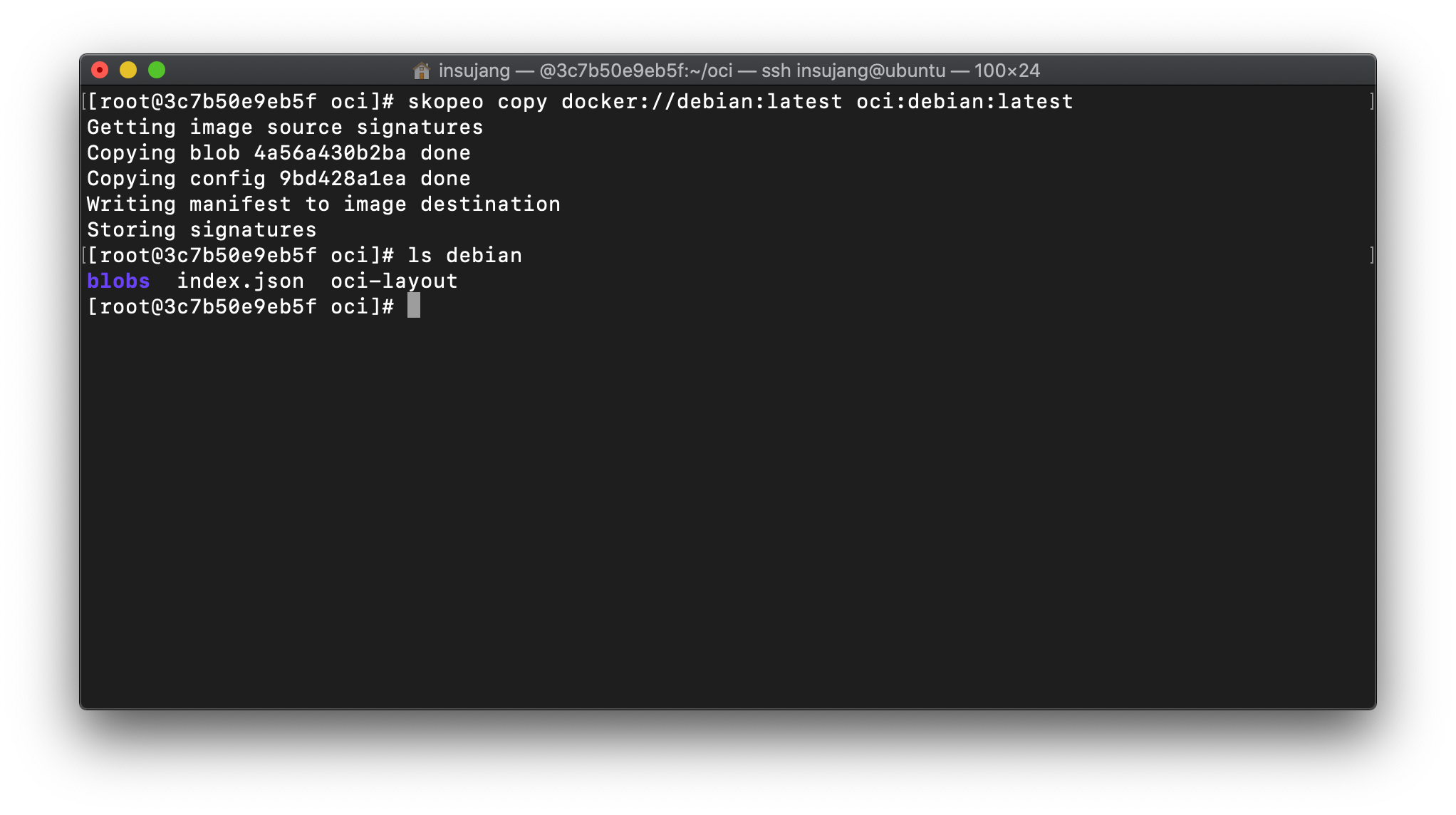
The OCI image consists of:
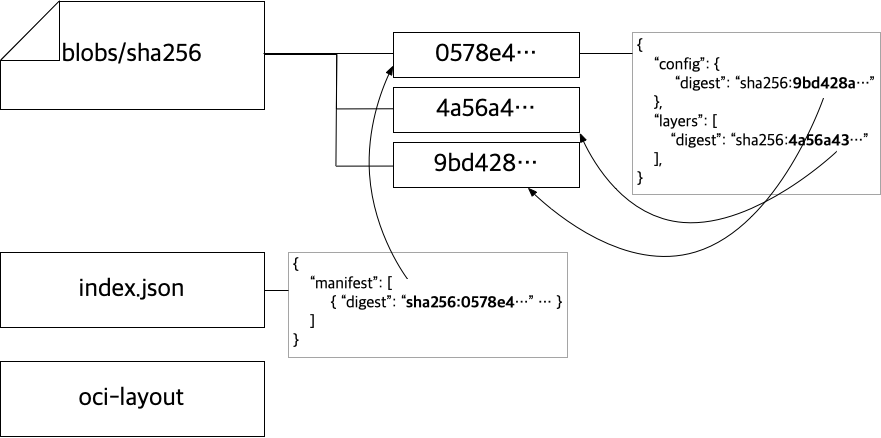
blobs/sha256: this directory contains information about image manifests and image layers, and compressed layer archives.index.json: this JSON plaintext contains information about the list of image manifests.oci-layout: this JSON plaintext contains the version of OCI layout… To be honest, I do not know how to use it.
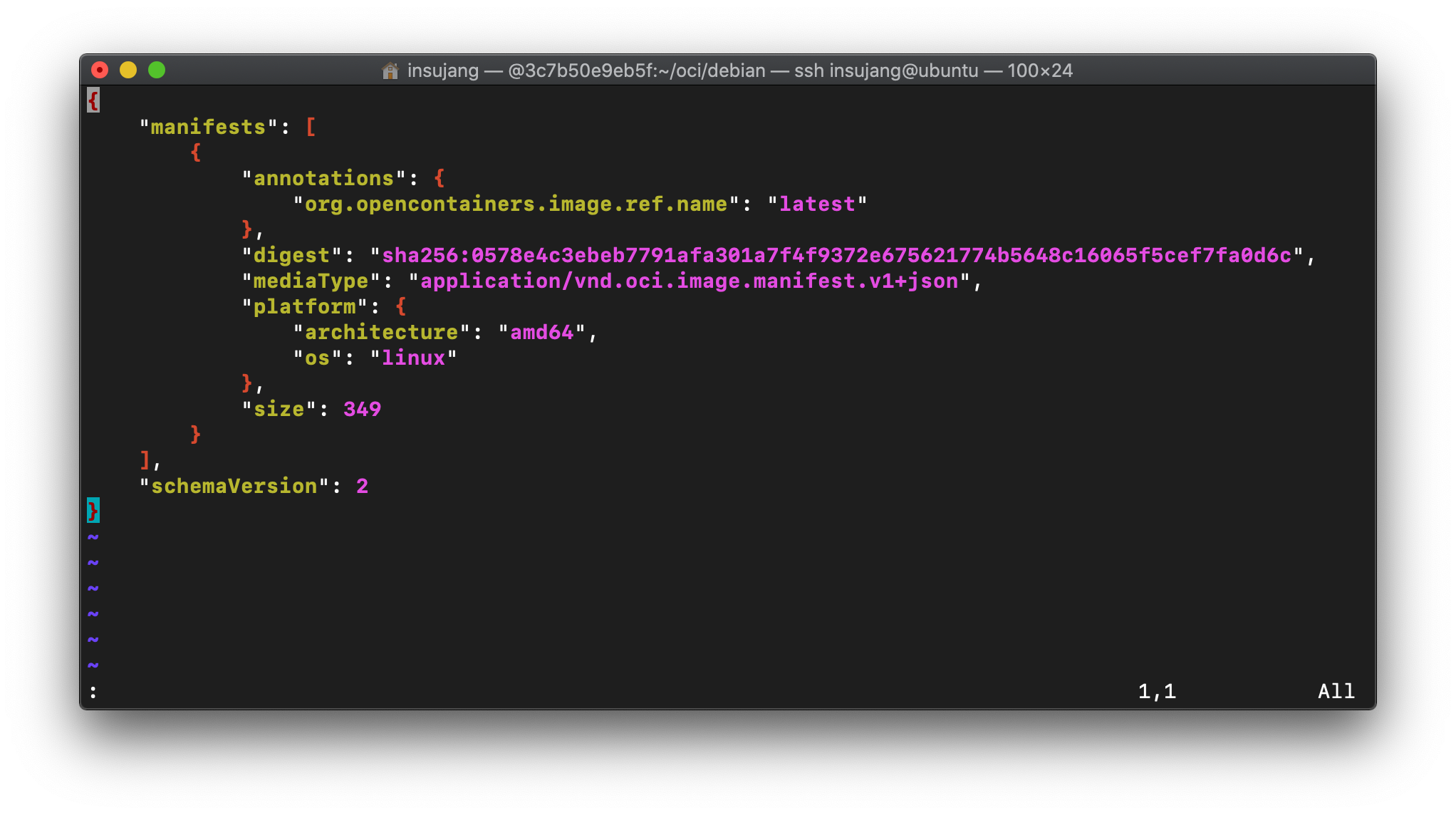
index.json of Debian OCI image.
anntations:org.opencontainers.image.ref.name usually represents a tag name [link].
Therefore, each OCI image directory can contain several image tags, all layers, manifests, configs of which are mixed in blobs/sha256 directory.
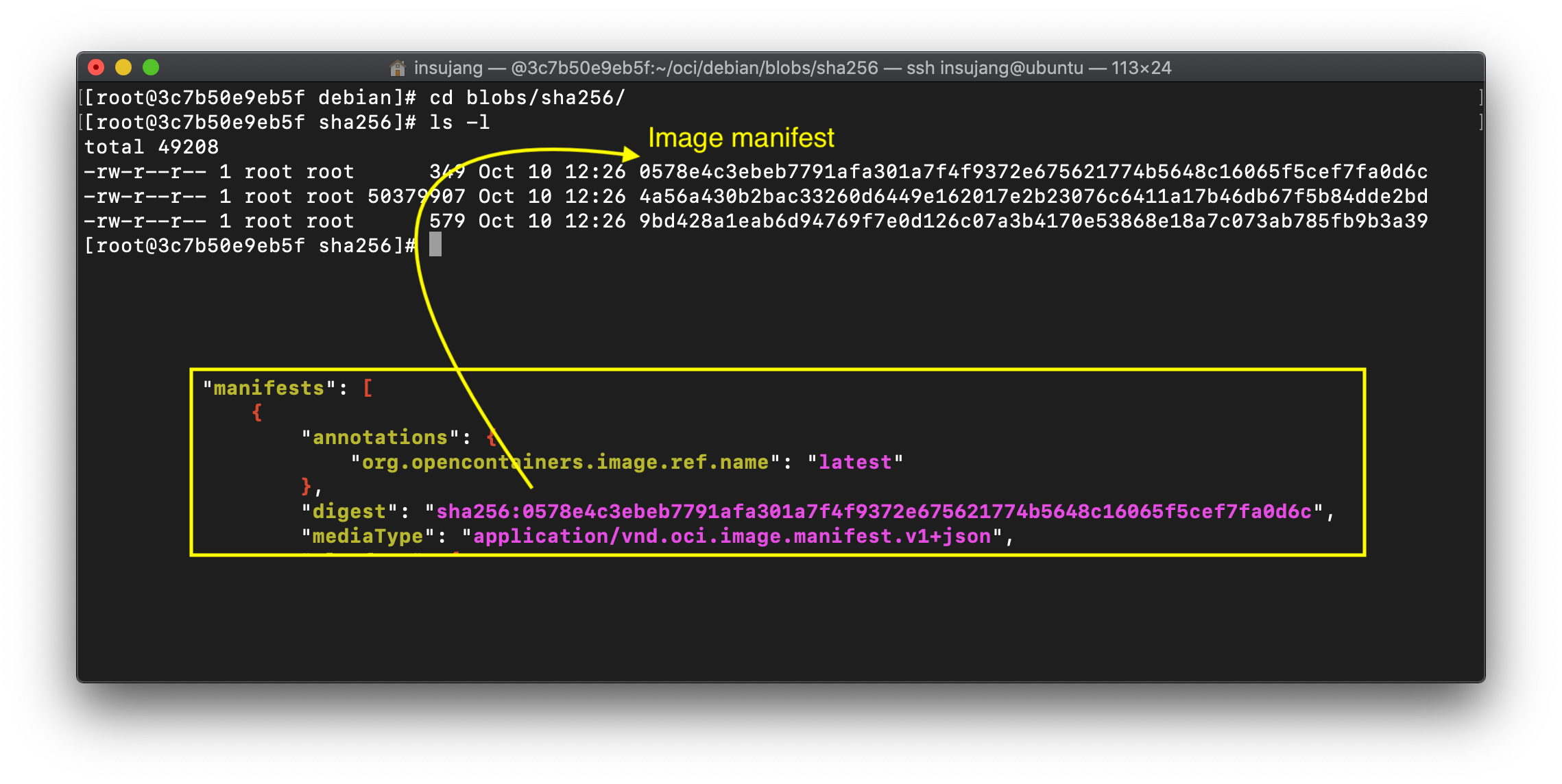
debian/blobs/sha256 directory. As indicated there is a file named with the digest sha256:0578... from index.json file.
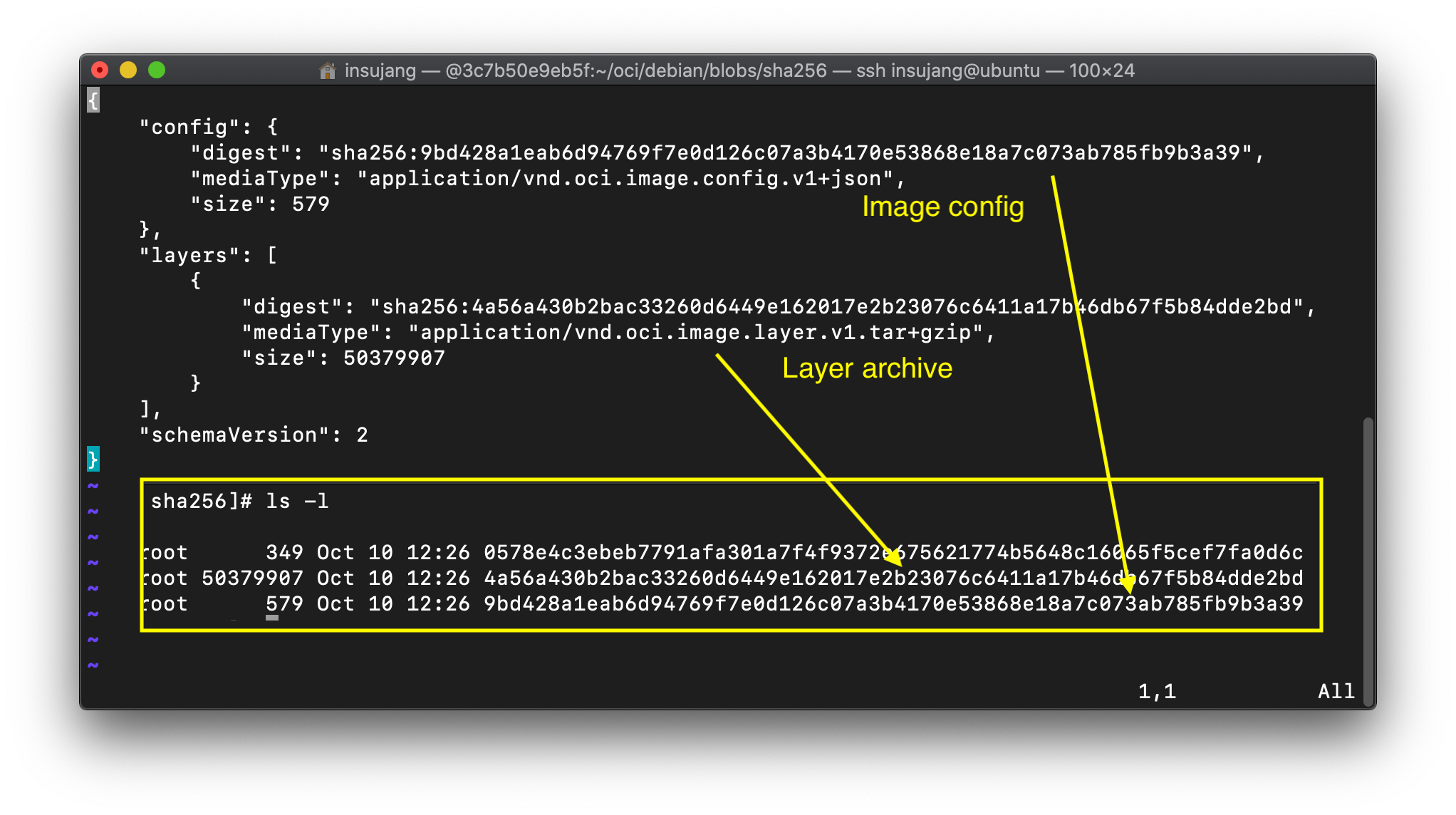
0578e4.... It explicitly defines the name of image config and layers. Those files are stored in the same directory with this manifest file.
As there is one tag in the image, contents of the directory blobs/sha256 is quite simple.
Runtime Spec #
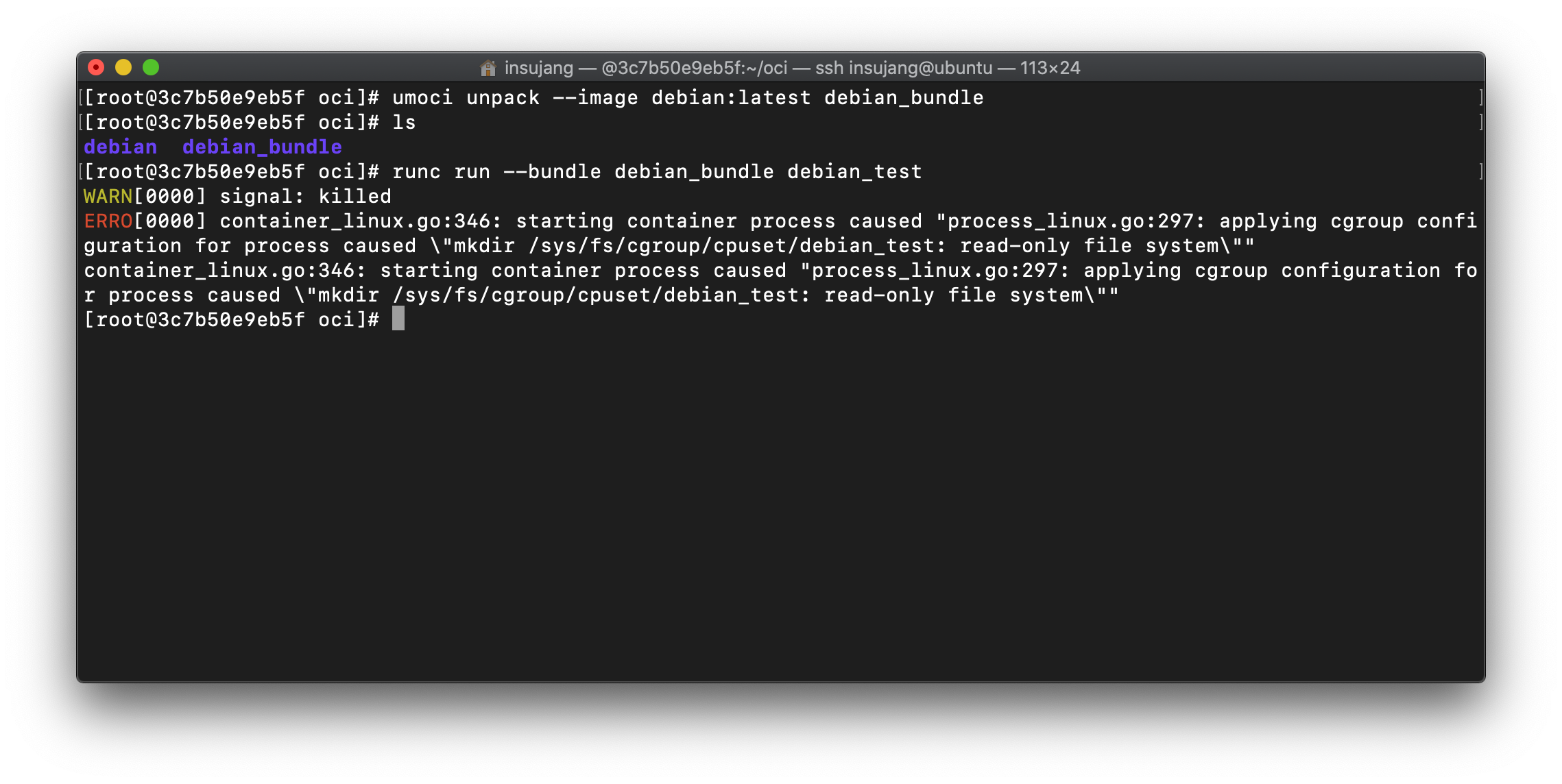
The OCI Image Spec is much similar to Docker images. Similar to Docker framework, where a container needs to be created from an image, a runtime bundle should be generated from the OCI image.
Detailed explanations are out of this post, just leave a link about it. There are several tools to unpack an OCI image and to generate an OCI runtime bundle.
With umoci or OCI image tool, we can unpack an OCI image to make a OCI runtime. And then, we can run a container with runc.